In recent months, PostgreSQL databases have become a prime target for cryptocurrency mining operations, highlighting the growing trend of cryptojacking. This unauthorized use of computing resources to mine cryptocurrencies not only threatens organizations financially but also underscores broader cybersecurity challenges.
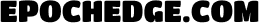
One of the most concerning threats is the PG_MEM malware, which exploits weak passwords in PostgreSQL databases to install cryptocurrency mining software. This malware employs brute-force attacks to gain access, leveraging the database’s “COPY... FROM PROGRAM” SQL command to execute arbitrary shell commands. Once inside, attackers can download and execute mining payloads, using techniques like creating new user roles with high privileges and modifying system configurations to maintain persistence.
Another evolving threat is the use of fileless malware, such as PyLoose, which targets cloud workloads by loading an XMRig miner directly into memory. This approach avoids traditional file-based detections, making it particularly challenging to identify and mitigate. Fileless attacks are becoming more sophisticated, often using Linux techniques like memfd to hide malware in memory, thereby evading detection by most security solutions.
The recent campaign targeting PostgreSQL servers demonstrates how attackers are adapting their methods. Over 1,500 servers have been compromised, with the threat actor using defense evasion techniques like deploying unique binaries for each target. This campaign exploits not only weak passwords but also misconfigured databases exposed to the internet, highlighting the need for better security practices.
Beyond the technical implications, these attacks underscore broader security issues. Misconfigured databases and weak passwords are common vulnerabilities that can be easily exploited. Organizations must prioritize robust network security measures, including using strong passwords, firewalls, VPNs, and intrusion detection systems.
As technology evolves, so do the methods of attackers. The future of cybersecurity will likely involve more sophisticated fileless attacks and AI-enhanced detection systems. Ensuring that databases are properly secured and monitored will be critical in preventing such unauthorized activities.
In the broader technological landscape, the strategic use of cloud environments can both enhance security and introduce new vulnerabilities. Cloud providers are increasingly offering tools like workload scanners to detect publicly exposed services with weak credentials, but the onus remains on organizations to implement these safeguards effectively.
Reflecting on these trends, it’s clear that technology not only offers powerful tools but also demands heightened vigilance. As more devices become connected and data-driven, the challenge will be to balance openness with security without stifling innovation. For now, the question remains: How will organizations and individuals adapt to these emerging threats while ensuring that technology continues to support, rather than undermine, societal progress? Explore more on these evolving trends in cybersecurity and technology at Epochedge.